INTRODUCTION
DarkTower recently identified and has been monitoring the use of OTP bots, available for
purchase in high-traffic Telegram fraud Group Chats.
FINDINGS
- DarkTower identified several OTP bots circulating.
- The bots can be used to circumvent Two-Factor Authentication by sending false requests
disguised as legitimate requests. - The bots are primarily sold and operated through Telegram.
INVESTIGATION
OTP bots, or One Time Password Bots, are used by threat actors to skim one-time passwords
from victims and to bypass two-factor authentication on compromised accounts. The bots
can be used by threat actors to access accounts that have been stolen or sold online. OTP
bots are primarily constructed via Telegram’s Bot API, which makes them difficult to analyze.
Stolen account credentials, often referred to as “fullz” in fraud communities, can be bought
and sold easily on dark web forums and within social media fraud groups. Once a client’s
account credentials have been obtained, threat actors will often need to bypass two-factor
authentication to access the account. By impersonating legitimate two factor authentication
requests, OTP bots can deceive victims into providing the needed verification codes for
accessing the stolen accounts.
Frequency
The screenshot below from the University of Alabama at Birmingham’s Computer Forensics
Research Laboratory shows that there are a dozen discussions on Telegram that mention the
term “OTP bot” at least two hundred times.

OTP Bot Usage
The bots are accessed through Telegram and are simple enough for relatively-
unsophisticated threat actors to employ. Below are two examples of bot user interfaces,
showing how the interaction looks to the fraudster using such a tool.

Figure 1 : OTP bot user interface seen on Telegram 1
Telegram user [@]no32bellz, similar to the watermark seen in the two images below, is User
ID 1575657773 and discusses OTP in his Channel called “official k3 Marketplace” with 63
Subscribers.

Figure 2 : Part 1 of 2–OTP bot user interface seen on Telegram

Figure 3 : Part 2 of 2–OTP bot user interface seen on Telegram
Threat actors do not need to have great technical skills to create one of these bots and use it.
Instead, many threat actors within DarkTower-monitored threat groups sell access to use
their OTP bots in exchange for monthly fees.
The figure below shows an instance of a threat actor selling access to an OTP bot via a
Telegram fraud Channel.
The same message was posted in at least two fraud Group Chats on Telegram, including one
on 03OCT2021 by “Loki” with Handle [@]lokitheroototp with User ID 1954998551, in the
“Scamily” Group Chat. Scamily has 11,520 Members The user [@]nmotpbot is no longer valid
on Telegram, and there is evidence that other users reported it as a scam account.

Figure 4 : Telegram post advertising OTP bot
Often the bots include modules, attacks targeting specific platforms or institutions. The
preconfigured attacks provide a ready-to-use experience for purchasers. The bots are
typically sold through a subscription system. There are many distinct OTP bots, which makes
it difficult to source attacks to a particular threat actor, and even when sourced to a specific
bot, it is difficult to take action against the malicious actor through Telegram. There are also
software-based approaches to skimming OTP passwords targeting Android devices; however,
these are significantly less popular and more difficult to use.
Following are six additional examples of recent Telegram posts that advertise OTP bots. The
first example below offers a lifetime subscription for $130 and reveals modules for CashApp,
Chase, Coinbase, Instagram, Klarna, PayPal, Robinhood, Venmo, and Wells Fargo. The post
was made on 06OCT2021 by the “Woke Shop” user with handle [@]wokeshop and User ID
1881041716, who re-posted it from their own Channel that has 557 subscribers. They posted it
into the “AIO Crime” Group Chat that has 2,556 Members.

Figure 5 : hxxps://t[.]me/aiocrime2/105316
The following example reveals pricing and modules for Apple Pay, PayPal, and Samsung. It
was posted on 22NOV2021 in the Group Chat called “Sauce Money Gang” with 16,070
Members. The poster [@]harry_admin is User ID 1334868475.
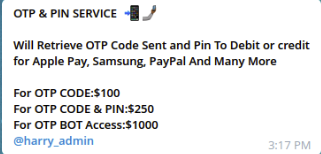
Figure 6 : hxxps://t[.]me/c/1494713926/154737
The following post was made in multiple Group Chats by user “Wan Don” with handle
[@]wandon2002 and User ID 2143206648. The post below was made in the AIO Crime Group
Chat.

Figure 7 : hxxps://t[.]me/aiocrime2/122739
The following example was posted on 16NOV2021 by User ID 1982563267 in a Group Chat with
8,078 Members. The user’s profile reveals the contact phone +1 551-314-0331

Figure 8 : hxxps://t[.]me/DarksideForum/156750
The following example reveals more pricing details. It was posted on 16NOV2021 by User ID
1433399779 in the same Group Chat seen in Figure 8.

Figure 9 : hxxps://t[.]me/DarksideForum/156952
Posted on 20OCT2021 by User ID 2023578214 in a Group Chat with 5,653 Members:

Figure 10 : hxxps://t[.]me/paradisegroupchat/123629

